Hash Calculator
- Choose an algorithm (MD5 / SHA-1 / SHA-256 / SHA-384 / SHA-512).
- Paste or type your text into the input box.
- Copy the generated hash from the output box.
Help
FAQ
Is hashing the same as encryption?ShowHide
No. Hashing is one-way and cannot be decrypted back to the original text. Encryption is reversible with a key.
Which algorithm should I use?ShowHide
For security-related use cases, prefer SHA-256 or SHA-512. MD5 and SHA-1 are considered weak due to collision risks.
Why do I get different hashes for “the same” text?ShowHide
The input is likely not identical byte-for-byte. Newlines, extra spaces, casing, or different encodings can change the hash.
Can I use MD5/SHA to store passwords?ShowHide
Not recommended. Use a password hashing algorithm like bcrypt, scrypt, or Argon2 with a unique salt.
What is a checksum and how is it used?ShowHide
A checksum is a hash used to verify data integrity. You can compare a published checksum with the one computed from your file/text to detect tampering or corruption.
How to use this hash calculator
- Choose an algorithm (MD5 / SHA-1 / SHA-256 / SHA-384 / SHA-512).
- Paste or type your text into the input box.
- Copy the generated hash from the output box.
Privacy
Full guide
What is a hash (digest)?
A hash (also called a message digest) converts an input of any length into a fixed-length fingerprint.
Common properties:
- Same input → same output
- Small changes in input → very different output
- Designed to be one-way (you cannot reliably recover the original text)
When is a hash calculator useful?
Typical scenarios:
- Verify downloads: compare your computed hash with an official checksum.
- Deduplicate content: identical text produces identical digests.
- Integrity checks in pipelines: detect whether payloads changed.
- Request signatures: some APIs require hashing certain fields before signing (protocol-specific).
Examples
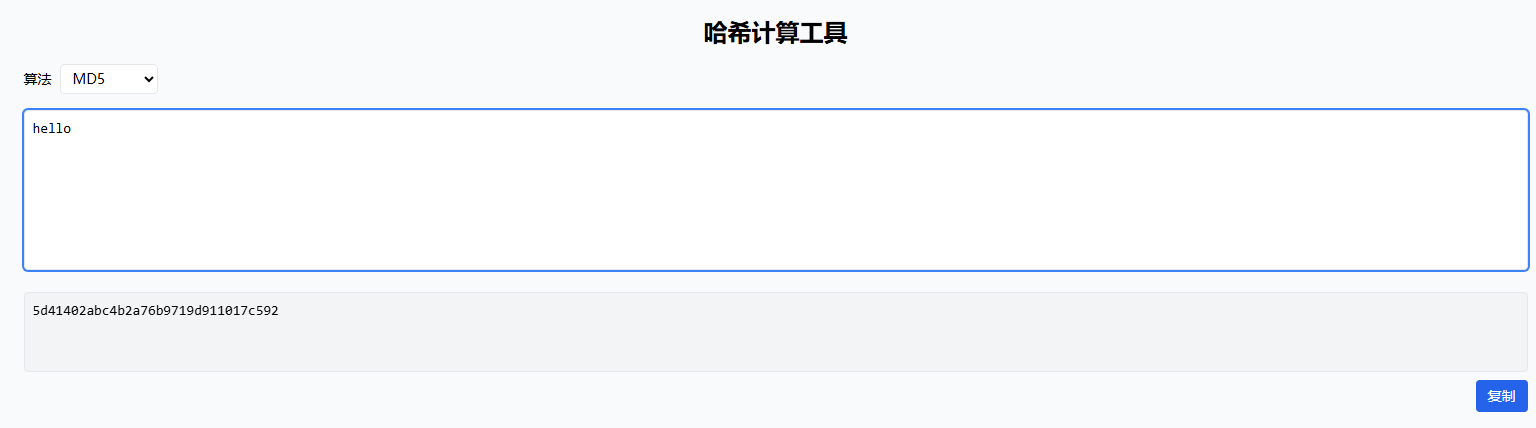
Example 1: Hash a simple string
Input hello with MD5 algorithm:
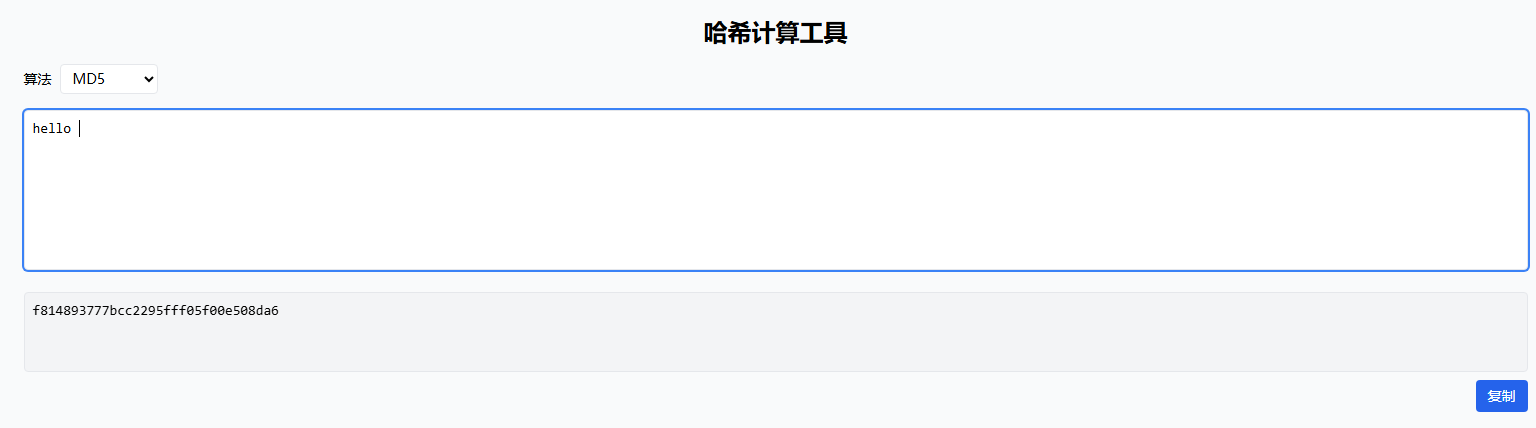
Example 2: Why whitespace matters
Input hello vs hello (with trailing space) — hashes are completely different:
Security notes (important)
- MD5 and SHA-1 are not recommended for security (collision attacks exist).
- A hash does not hide information. If the input is guessable (e.g. short passwords), attackers can brute-force it.
- For passwords, use dedicated password hashing (bcrypt / scrypt / Argon2) instead of MD5/SHA.
Troubleshooting
- If the result looks unexpected, check for:
- Hidden whitespace (spaces,
\n,\r\n) - Different casing (A vs a)
- Different normalization (e.g. Unicode characters)
- Hidden whitespace (spaces,
- Make sure you’re hashing exactly the intended input text.